Configure Connection between RSA and LDAP Server
The RSA must have valid credentials and access rights to make LDAP queries against the true LDAP instance. This relationship is managed within the configuration file of the RSA.
LDAP configuration will require the LDAP URL of the server the RSA is protecting. For a successful RSA <--> LDAP connection and data transfer, the following LDAP-specific parameters need to be configured:
ldap:
anonymous-read-only: false
urls: ldap://{ldap-url}:{port}/dc=example,dc=com
username: cn=read-only-admin,dc=example,dc=com
password: password
userDnPattern: uid={0}
keys:
- mail
- cn
- sn
The snippet above outlines a sample LDAP configuration that would be applied to the configuration file of the RSA.
| Configuration | Description |
|---|---|
| anonymous-read-only | Some LDAP server setups allow 'anonymous read-only access'. The RSA uses its own credentials to authenticate to an LDAP server, but we also need to authenticate a user to create a "Context" from which a search query will be made. This field, if set to 'false', will ensure that all LDAP queries made against an LDAP server will only be deemed acceptable as long as a known LDAP user is authenticated (as opposed to anonymous lookups) |
| urls | This consists of the following 3 values: 1) The LDAP protocol abiding host name of the LDAP server. 2) Port corresponding to the server URL. 3) Base domain name appended to the server URL. This serves as a base path/initial context that will be used to traverse and combined with the user DN (distinguished name) pattern will ultimately identify individual users within the LDAP tree. The example below uses "dc=example,dc=com" as the base path. |
| username and password | This information can be sourced from your LDAP or Active Directory team. Read-only Admin credentials will need to be provided where the username and password will correspond to the 'cn' (common name) value and the password value of the 'read-only' admin entry respectively within the LDAP Directory Information Tree. |
| userDnPattern | The userDnPattern property will enable the Spring LDAP authenticator to search and identify a user within the LDAP server. In this case, we are only using a single DN (Distinguished name) pattern. For example, if the username is 'edward' (provided at the Login page of the RSA), the DN used to bind to LDAP will be uid=edward relative to the initial context dc=example,dc=com. Even though the unique username provided at the login form was "edward", the actual name used to authenticate to LDAP will be the full DN 'uid=edward,dc=example,dc=com'. It is important to note that the userDnPattern MUST match the userDnPattern set within the LDAP server. For example, if the LDAP tree identifies unique users using "cn", ldap.userDnPattern within the RSA-LDAP configuration file must be set to cn={0} instead of uid={0}. |
| keys | The 'keys' attribute here represents a list of all LDAP attributes that will be pulled from the LDAP server and sent back in a valid successful response to a valid authorized userinfo request at the RSA. Note: Though the list of attributes is configurable, these attributes MUST be available at the LDAP server itself. |
Enabling Self-Hosted Authentication
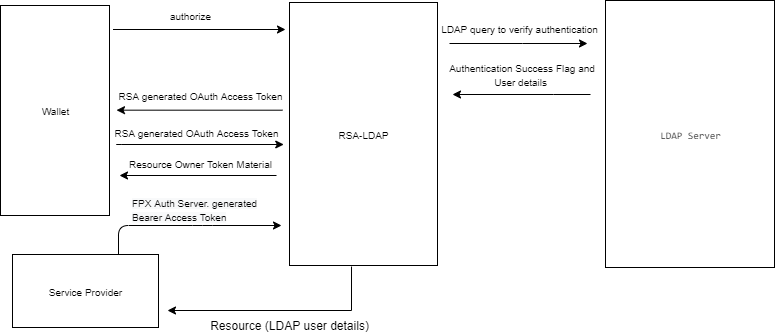
The LDAP version of the RSA self-hosts user authentication and stores user details it receives from the LDAP Server (upon successful authentication).
Within the configuration file, fpx.oidc.provider.self-hosted must be true and fpx.oidc.provider.federated must be false. This ensures that authentication (for connecting a resource owner with the data-source/RSA of their choice) is handled by the RSA itself and not federated off to a 3rd Party Provider.
fpx:
oidc:
provider:
self-hosted:
enabled: true
federated:
enabled: false